Unlock the secrets behind smart lock features most people misread and discover what truly keeps your home secure and convenient.
Browsing Category
Technology
59 posts
Smart Lock Buying Mistakes: The Costly Errors Most Shoppers Make
Keen to avoid costly smart lock mistakes? Discover essential tips to ensure security, compatibility, and peace of mind before you buy.
How To Choose a Smart Lock: The Details Most Buyers Miss
Smart locks offer convenience and security, but understanding key features and pitfalls can make all the difference—discover what most buyers miss.
Smart Lock Benefits For Front Door Safety: The Overlooked Advantages That Matter in Real Life
Knowledge of smart lock benefits reveals overlooked safety features that could transform your home security—discover what truly matters in real life.
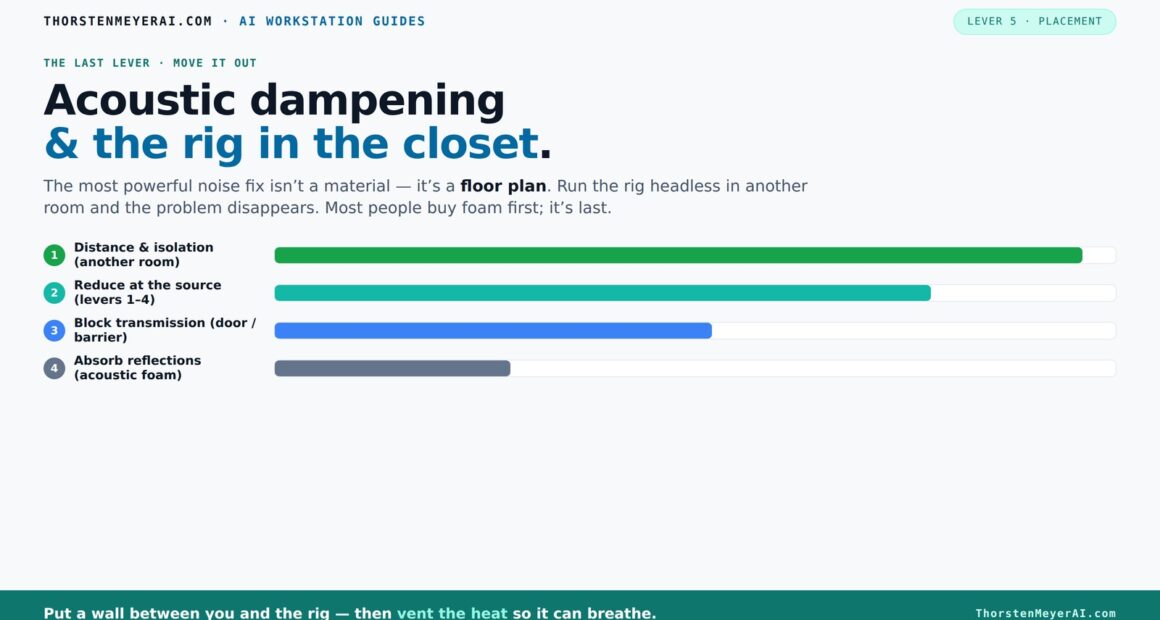
Acoustic Dampening, Placement, and the “Rig in the Closet” Setup
Learn how to optimize your closet setup for quiet, clear recordings. Discover placement, dampening tricks, and the real limits of closet rigs.
Build vs Buy a Prebuilt AI Workstation
Deciding between building or buying a prebuilt AI workstation? Discover the real costs, performance factors, and support options to make the right choice in 2026.
One Video In, a Whole Publishing Kit Out — Without the Cloud
Discover how offline-first workflows turn a single video into a full publishing kit—embodying speed, control, and privacy without relying on cloud services.
Who Should Buy a Smart Ring? The Use Cases That Actually Make Sense
Proactive individuals seeking discreet health monitoring and seamless connectivity will find smart rings a practical choice—discover if this wearable fits your lifestyle.
Smart Ring Setup Tips: The Small Fixes That Change Everything
Unlock the secrets to seamless smart ring setup with small fixes that can transform your experience—discover what you might be missing.
Smart Ring Features That Matter: The Specs Most People Misread
Learn which key smart ring features are often misunderstood and why understanding these specs is crucial for making the right choice.